Research Summary
Interests
- Security & Privacy
- Machine Learning
- Online Social Networks
- Distributed Systems
- Abuse Detection
- AI for Social Good

“Companies spend millions of dollars on firewalls, encryption, and secure access devices, and its money wasted; none of these measures address the weakest link in the security chain.” – Kevin Mitnick

Connection relations in Online Social Networks (OSNs) have been used by attackers to access private and sensitive user data, post false or abusive information on the timelines and news feeds of victims, and scam and influence the perceptions of victims. The massive growth of social media usage has incentivized perpetrators to connect users through identity deception, which is often successful due to the lack of adequate verification of declared information. The goal of this project is to significantly expand the understanding of identity deception and abuse in online social networks, and design and build intervention mechanisms that would render these types of attacks unsuccessful. This project will involve users in creating a digital framework that can educate them about the sockpuppet attack and encourage them to carefully examine their connection invites before accepting or declining them, and stay away from accepting invitations from suspicious accounts. The study of online social network sockpuppet requests will help develop and validate, a new generation of sockpuppet prevention solutions. This has the potential to help protect millions of vulnerable OSN users from sexual predators, online fraudsters, scammers, adversaries, or even malicious hackers.
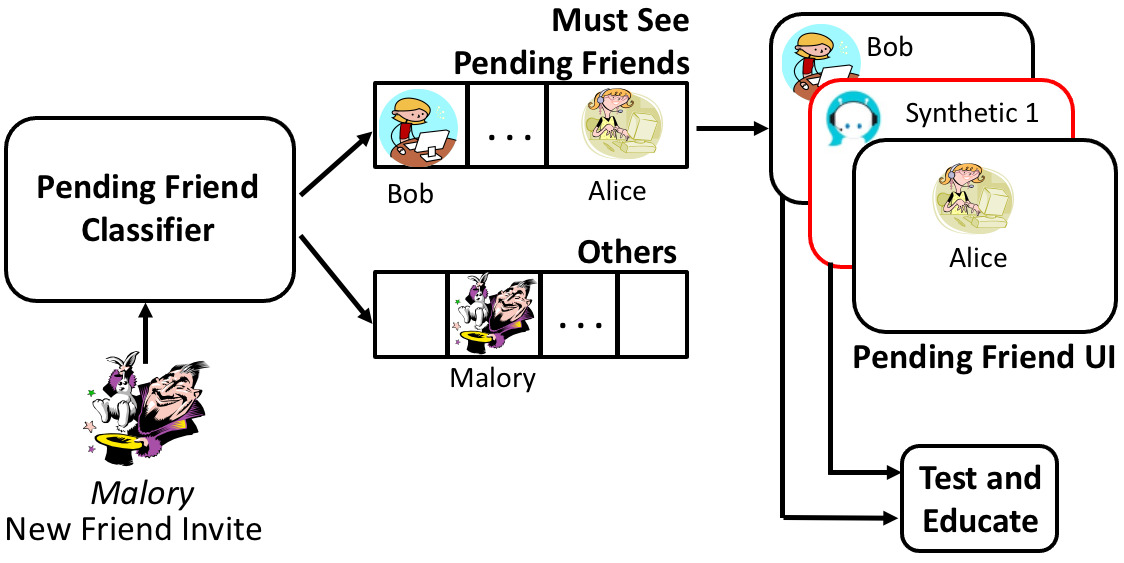
This project will build a digital framework rooted in cognitive psychology, UX research, and machine learning methods to defend against sockpuppet connection requests in online social networks. In a first research thrust, the researchers will develop survey instruments and user studies to investigate the pending connection decisions, motivations, and behaviors in OSNs. The researchers will also develop an app platform, to collect detailed, ground truth behavior data from OSN users, and provide an evaluation environment for the proposed solutions against a control app. The findings from this research thrust will be utilized to develop the next thrust, where the researchers will implement a "spam connection" folder through a pending connection decision classifier. Finally, the researchers will integrate sockpuppet education and motivation to develop a novel Online Social Network Pending Connection Processing Interface (OSN-PCPI). This not only will enhance the understanding of just-in-time motivations and behaviors related to social network risks, but will also help sociologists gain deeper insights from underexplored social and spatial dimensions provided by social networks to test relevant theories.
This project is supported by the following NSF grant.

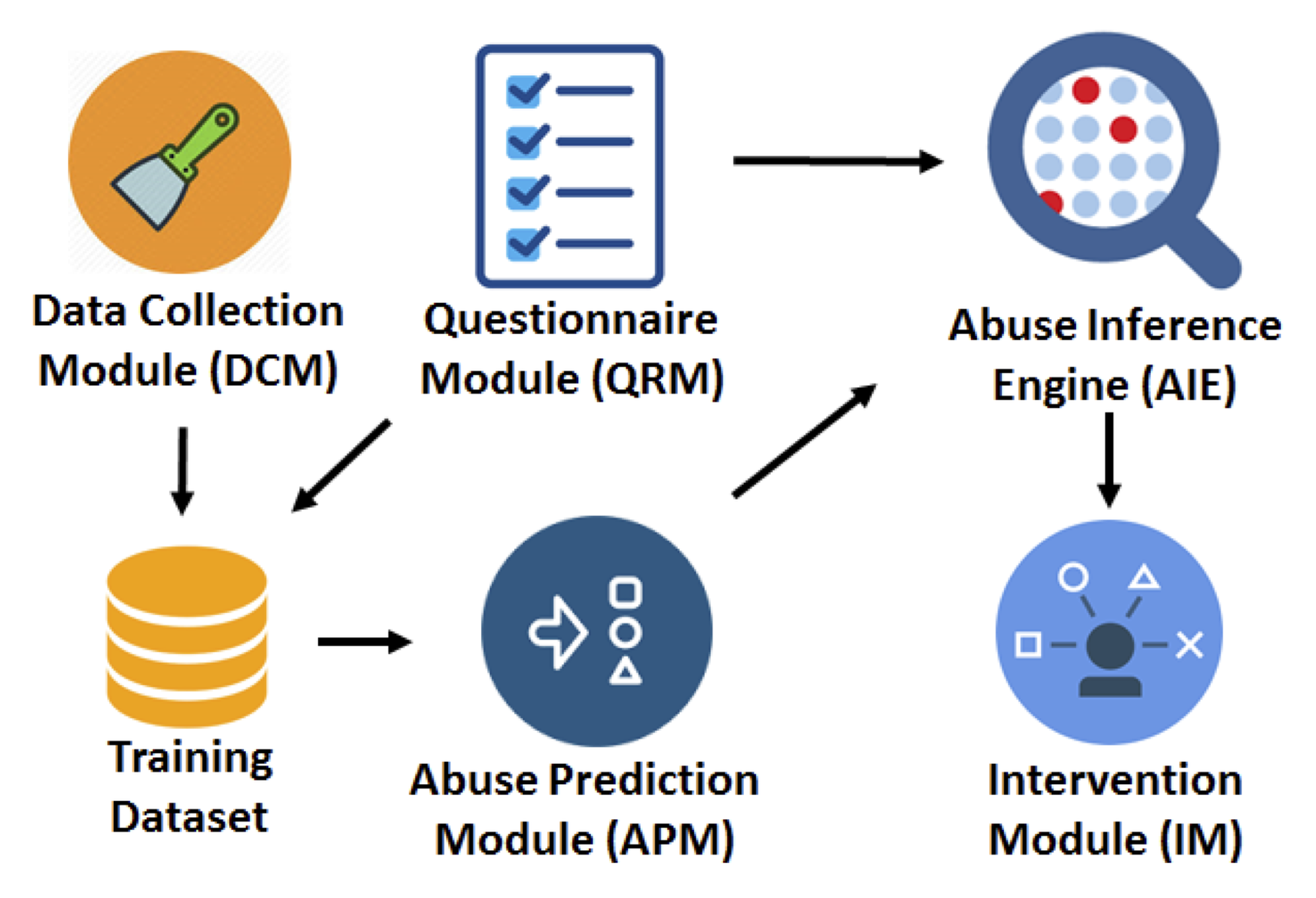
In our research, we sought to develop an automated social network abuse detection system which is able to reduce the attack surface of its users, by reducing the number of, or isolating friends predicted to be perceived as potential attack vectors. This presents a substantial challenge as adversaries leverage social network friend relationships to collect sensitive data from users and target them with abuse that includes fake news, cyberbullying, malware, and propaganda. We leverage these findings to develop AbuSniff (Abuse from Social Network Friends), a system that evaluates, predicts and protects users against perceived friend abuse by suggesting several personalized defensive actions for such friends. We began by developing the first ever mobile app questionnaire, that can detect perceived strangers and friend abusers. To replace the questionnaire, we then introduced mutual Facebook activity features that have statistically significant overall association with the AbuSniff decision and showed that they can train supervised learning algorithms to predict questionnaire responses using 10-fold cross validation. We trained our system with several supervised learning algorithms, including Random Forest (RF), Decision Trees (DT), SVM, PART, SimpleLogistic, MultiClassClassifier, K-Nearest Neighbors (KNN) and Naive Bayes and chose the best performing algorithm for predicting each of the questionnaire questions.
Our approach provides a method to evaluate AbuSniff system through online experiments with participants recruited from the crowdsourcing site from 25 countries across 6 continents. Results showed that the questionnaire based AbuSniff was significantly more efficient than control in terms of participant willingness to unfriend, sandbox and restrict abusive friends. The predictive version of AbuSniff was highly accurate (F-Measure up-to 97.3%) in predicting strangers or abusive friends and participants agreed to take the AbuSniff suggested actions in 78% of the cases. When compared to a control app, AbuSniff significantly increased the participant self-reported willingness to reject invitations from strangers and abusers, their awareness of friend abuse implications and their perceived protection from friend abuse.
This project was supported by three NSF grants.
Our solution and results have been widely cited, that include some very prominent studies, including the following:
We have also received email communications from researchers at Seoul National University from South Korea, who were impressed with our methodology and are using our method of built-in app to pre-classify and inform abusive friends in their ongoing (unpublished) work.
Lastly, We have been in communication with the researchers from Facebook Research, who were impressed with my research and invited me in the Facebook headquarter to discuss our project.

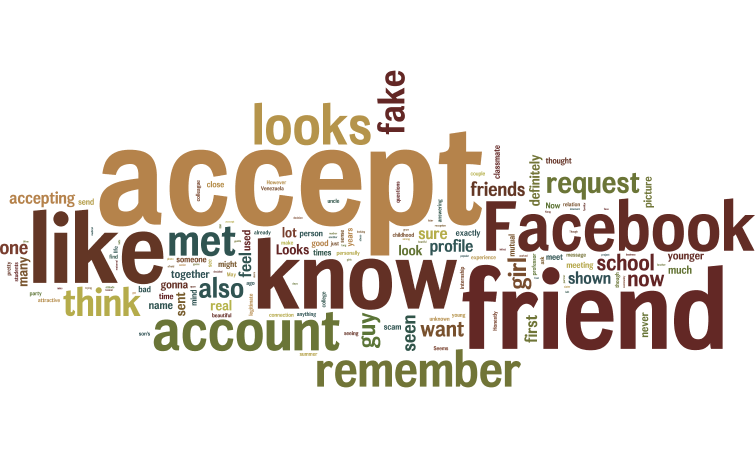
In our research, we sought to develop defenses against social network friend spam. Friend relationship is the largest gateway for attackers in Facebook and Twitter to collect personal data from victim accounts that are befriended, and use it to infer other sensitive user information, perform profile cloning, sextorsion, identity theft, and spear phishing attacks. Attackers often send friend spam requests to social network users in the hope of being accepted as data and posts are often shared by default with user’s friends. We began by performing interview and online studies using our developed apps, that can send friend requests from synthetic fake accounts, which confirmed that Facebook users are highly vulnerable to friend spam. To solve this problem, we introduced FLock, a new design to view and process received friend invitations, that encourages users to investigate pending friends. We further introduced T-FLock, a FLock extension that further trains users to be aware of friend spam. To help determine user vulnerability to friend spam without requiring user interaction, we developed a classifier to predict user decisions on pending friend invites. To train and test our classifier, we used k-fold cross-validation for time series, where we train on the first k decisions of each user, and test on the rest of the invitations, k is between 1 and the maximum number of pending friends per participant. Even when trained with only 5 past user decisions, our decision predictor achieved an F1 score of 83.43%.
Our approach provides a method using FLock and T-FLock to leverage the users as the first line of defense instead of forensically detecting friend spam, by involving them in the spam detection process, at the time when the spam attack takes place. In studies with 120 online participants, we found that when compared to a control Facebook-like interface, T-FLock and FLock significantly reduced the percentage of confirmed synthetic friends, increased the number of inspected synthetic friend profiles, and decreased the percentage of blind confirms. Our predictor can be used to detect fake accounts, and implement a spam invitation folder, similar in concept to spam e-mail folders, to help users better negotiate and regulate their relationship boundaries.
This project was supported by three NSF grants.

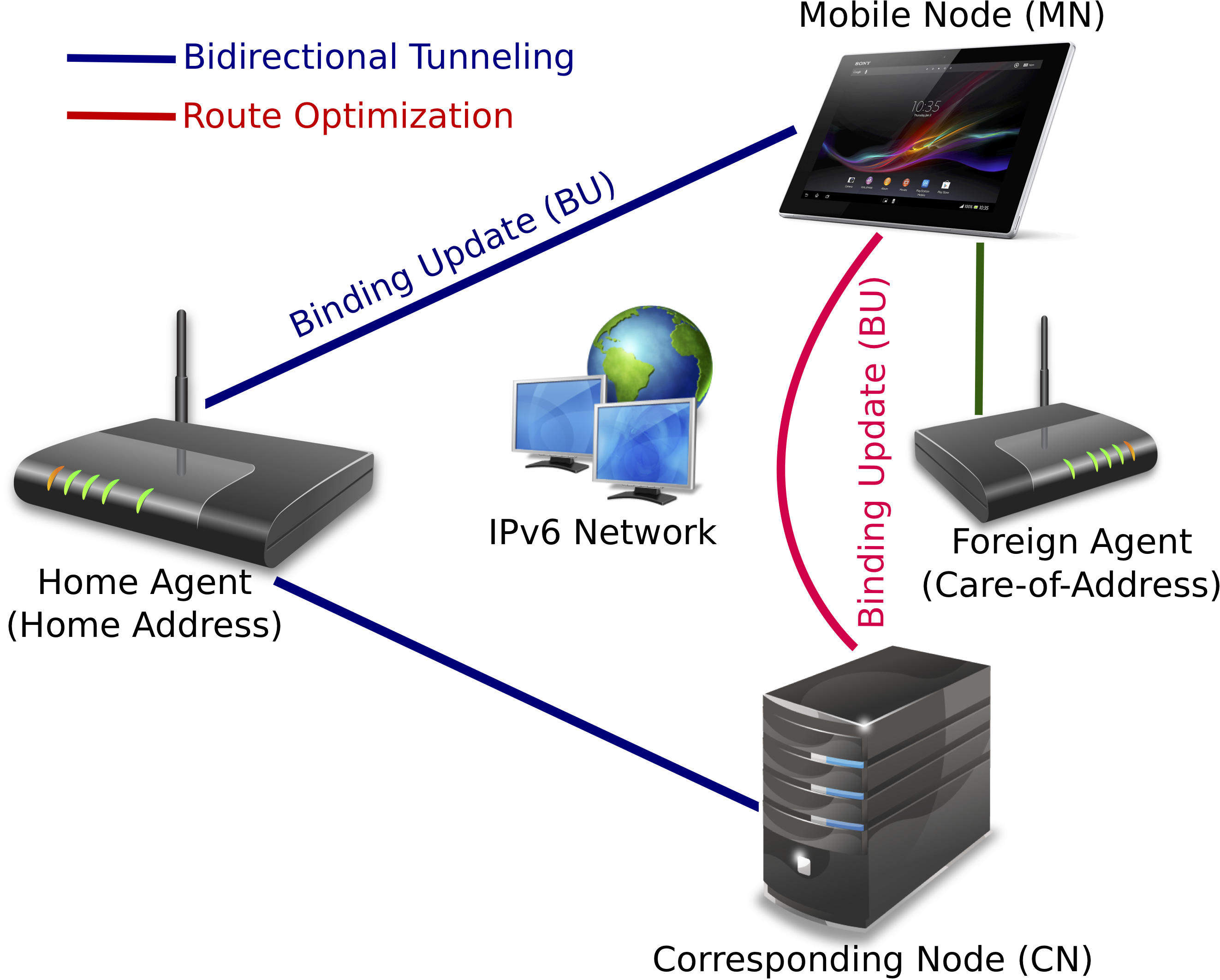
In our research, we sought to develop a method to model four well-known Mobile IP attacks, such as Denial-of-Service (DoS) attack, bombing attack, redirection attack and replay attack with Stochastic Game Petri Net (SGPN). The urging need for seamless connectivity in mobile environment has contributed to the rapid expansion of Mobile IP. Mobile Node that changes its IP address needs to update its care-of-address and send the binding update to the Corresponding Node. Binding updates are vulnerable to various attacks since Malicious Node can penetrate the route between Mobile Node and Corresponding Node. All of the attacks happen mostly during various phases of route optimization between the Mobile Node and Corresponding Node. We began by modeling the aforementioned attacks with SGPN. Next, we proposed mixed strategy based defense strategies for each of the aforementioned attacks and modeled them with SGPN. Finally, we calculated the Nash Equilibrium of the attacker-defender game and thereby obtained the steady state probability of the vulnerable attack states.
Our approach provides a method for understanding and modeling the well-known Mobile IP attacks and their appropriate defense strategies. We propose mixed strategy based defense strategies for the given attacks and evaluate the models by calculating the steady state probability of the vulnerable attack states. For that, we proposed an algorithm to calculate the steady state probability from the Nash Equilibrium in the SGPN. We showed that, under the optimal strategy, an IDS needs to remain active 72.4%, 70%, 68.4% and 66.6% of the time to restrict the attacker’s success rate to 8.5%, 6.4%, 7.2% and 8.3% respectively for the aforementioned attacks, thus performing better than many of the state-of-the-art approach.
Our solution and results have been widely cited, that include some very prominent studies, including the following:
We have also received email communications from researchers at University of Texas, who were impressed with our methodology and are using our method to develop an efficient Intrusion Detection System (IDS) in their ongoing (unpublished) work.

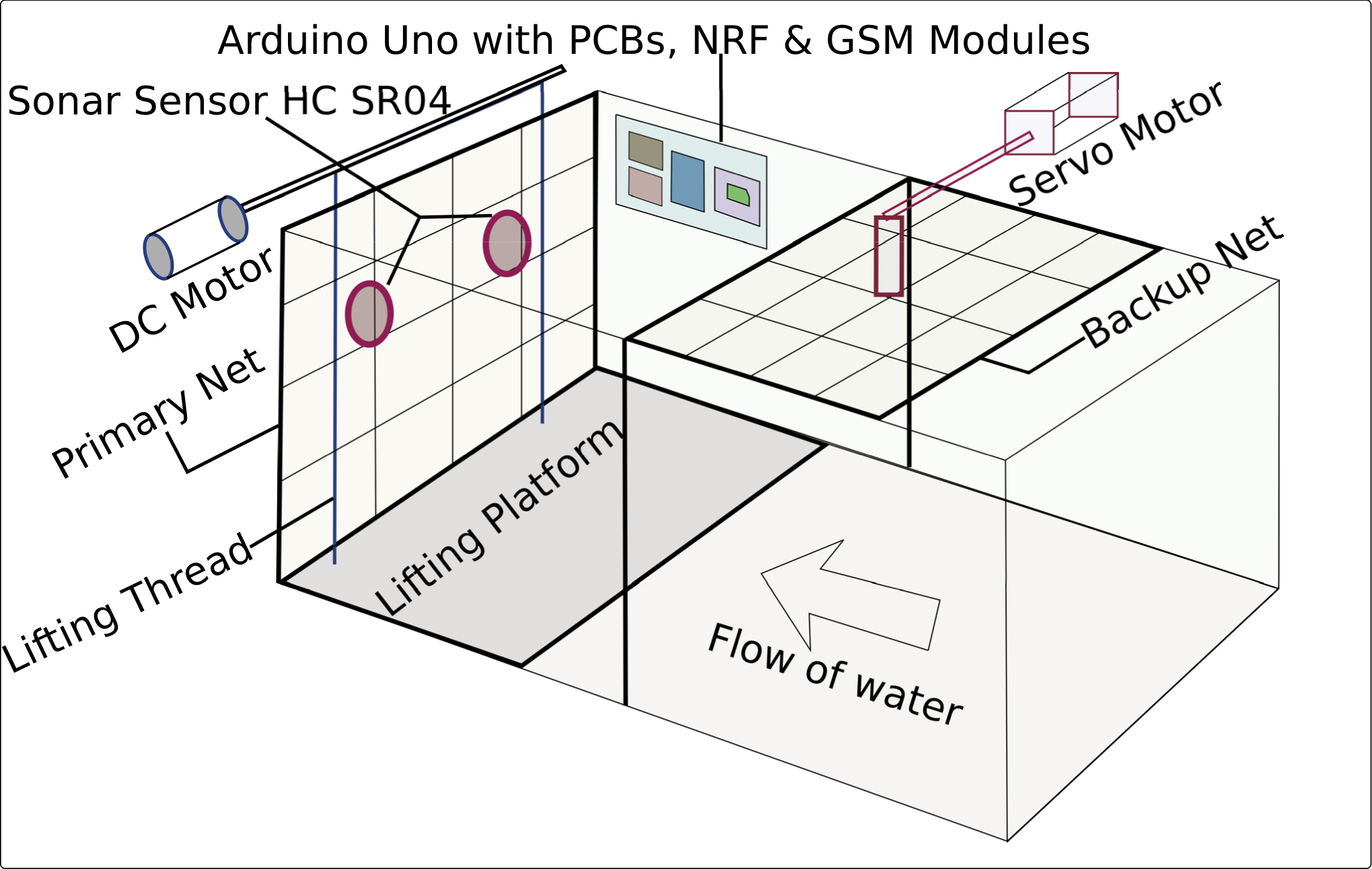
In our research, we sought to develop a method to design an automated sewerage management system that uses Arduino microcontroller coupled with an ultrasonic sensor, an NRF module and a GSM module to automate the routine checkup and removal of sewerage blockage in the big cities. This presents a substantial challenge for the big cities as sewerage blockage removal is vital for the continuous wastewater flow. We began by developing a blockage detection system consisting of an Arduino Uno board coupled with an NRF module, an ultrasonic sensor and a servo motor along with its power supply which could be placed inside the drain. As the waste material piles up on the lifting platform and crosses a certain height, the ultrasonic sensor detects the waste obstruction and triggers the NRF module and the servo motor, which in turn activates the blockage removal system. During the blockage removal process, the servo motor drives the backup net to place vertically through the drain so that further waste doesn’t get onto the lifting platform. The blockage removal system consists of a GSM module and a DC motor, guided by a track which lifts the platform containing waste materials to ground level with the help of lifting thread and pours the wastage on a waste container placed outside the drain. Once the waste container is filled, the GSM module sends text message to the city corporation control center for the collection and removal of waste.
Our approach provides a method for replacing the sewerage management system of cities having limited resources with an automated system. To the best of our knowledge, our method is the first attempt to use a microcontroller-based solution to design a fully automated sewerage management system. Our pilot study with the USenSewer prototype in a big city (Dhaka) has outperformed the state-of-the-art solutions, both in terms of cost and efficiency. Additionally, the system is very much scalable as we can use as many systems as needed without bothering the capacity of the control center.
Our solution and results have been widely cited, that include some very prominent studies, including the following:

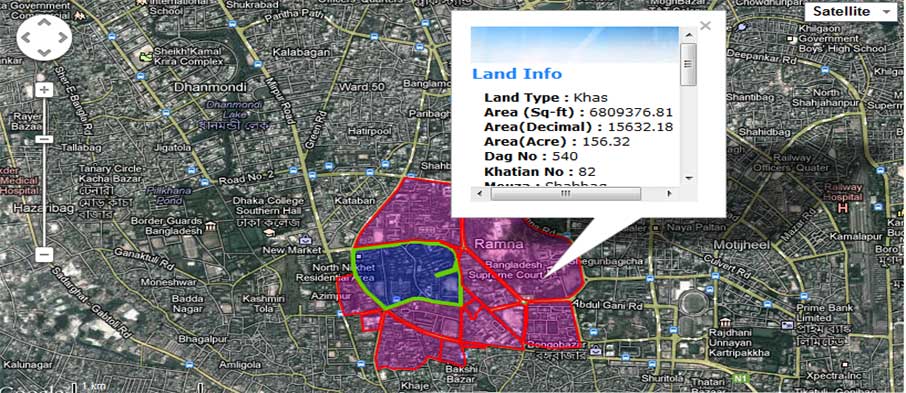
In our research, we sought to develop a model land management solution which offers a GPS based land surveying tool and an online land management system that encompasses an assortment of web based participatory services. Land management in third world countries presents a substantial challenge due the lack of technological resources and efficient infrastructure, thus requiring simple yet scalable digital innovations. We began by implementing the first ever GPS based land surveying tool that can be used for lower accuracy land surveying. Our tool was able to automatically generate land map directly from the GPS coordinate inputs that used geometric polygon overlay in Google Maps. Using this tool, we created a MySQL database of Dhaka city lands that also included the ownership information. Based on this database, we developed a highly scalable and large web application using Codeigniter PHP framework that offered superb speed, maintainability and agility. We designed a high load architecture that featured separate web, database and file servers along with task queues and DNS balancing. we also developed mobile clients using RESTful API for both the landowners and the land office employees.
Our approach provides the landowners an easily accessible way to search land, buy/sell land, advertise/bid, update map, pay land tax, resolve dispute and generate land deed. We also performed a feasibility analysis and compared the results with the existing traditional system. Our results showed that the proposed system significantly improved the traditional system's productivity and service availability and highly reduced the need for manpower resources.
Our solution and results have been widely cited and implemented, that include some very prominent studies, including the following:
A multilingual and multifunctional media player based on Java SE.
(Java)
Automated the consular services, central receipt and diplomatic bag sections of MOFA, Bangladesh.
Successfully implemented & tested software for govt. services.
(C++, Java, Bootstrap, CodeIgniter, MySQL)
Designed and developed a secure, fully transactional and customizable e-commerce platform.
Eboighar currently has 10 million active users.
(PHP, Bootstrap, CodeIgniter, PostgreSQL)
A complete digital notebook solution.
(C)